Since its inception, Eazfuscator.NET has offered the ability to encrypt the names of types, members, and other assembly symbols with a secret password.
Once encryption is applied, the assembly remains obfuscated but the original symbol names can be retrieved back whenever such neccessity arises.
The most common usage scenario is to decode an obfuscated stack trace back to its original form:
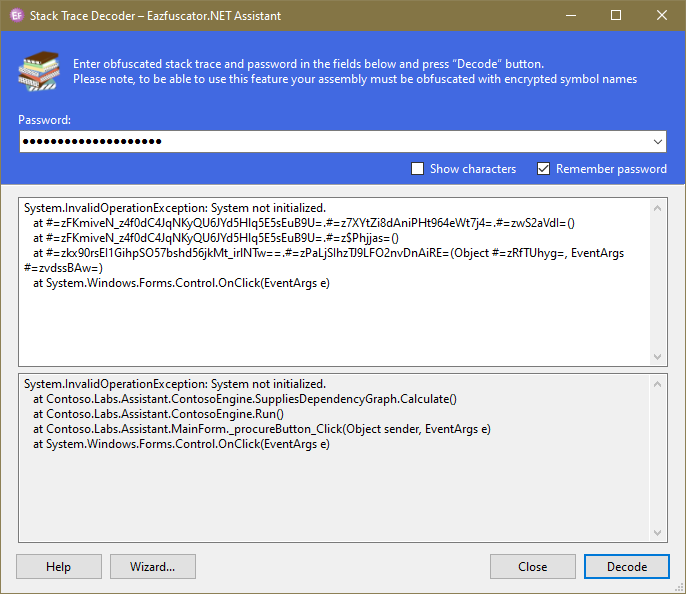
Hence the umbrella name of that feature: stack trace decoding. It allows to decode a stack trace using a piece of prior knowledge such as stack trace password.
In contrast to its numerous rivals, Eazfuscator.NET neither uses database nor mapping files. This signigicantly simplifies the handling of obfuscated assemblies as there is no separate state to store or manage. Instead, there is a password and that's all it takes.
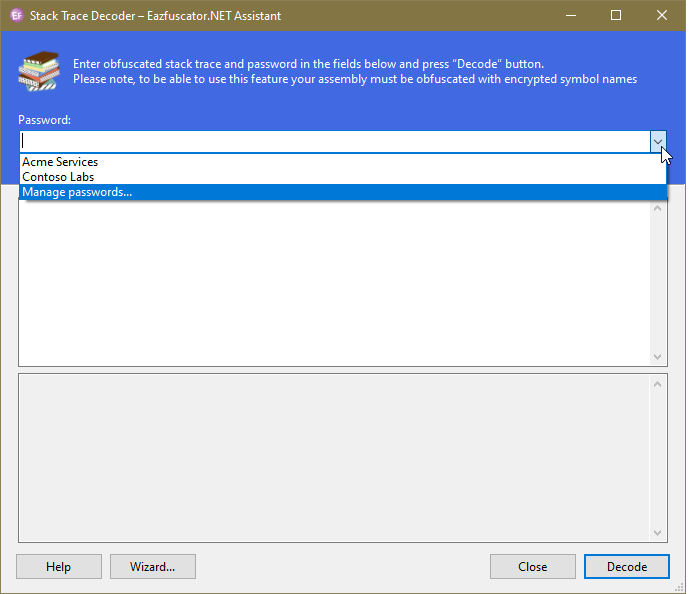
From security standpoint, you may prefer to use several stack trace passwords. One password per product is a good general approach. Naturally, you have to remember which password corresponds to which product; thus switching between products may take some extra time and effort.
To make this process easier, Eazfuscator.NET 2020.4 offers a built-in management of stack trace passwords:
The list of predefined passwords is the basis of the password management:
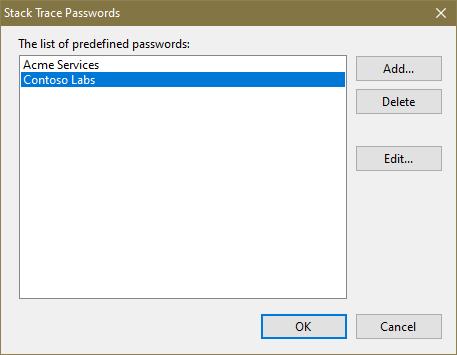
The dialog allows to manipulate the predefined passwords in every conceivable way. Once defined, passwords can be quickly reused in the password text box.